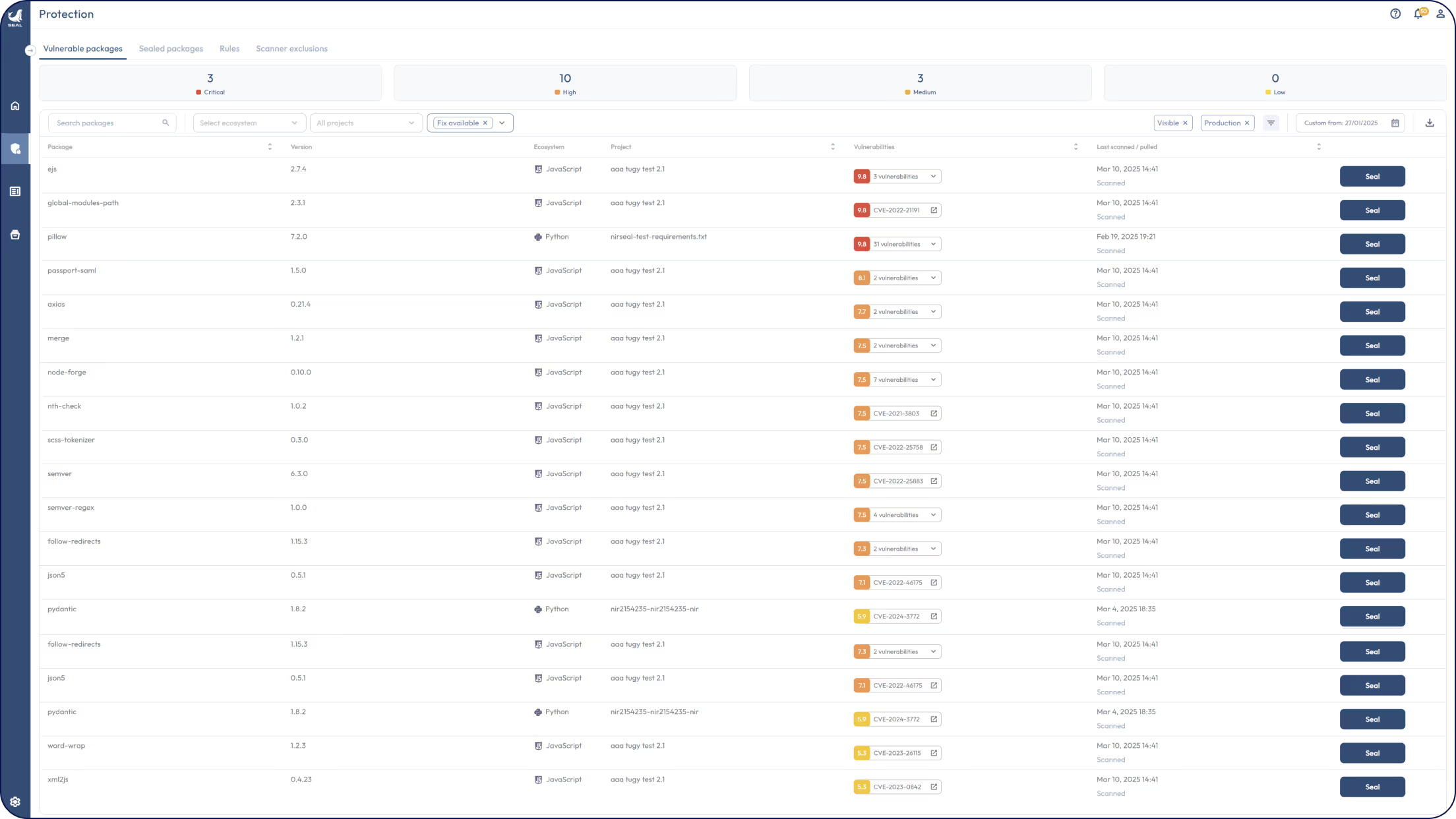
Fix CVEs in open source software without breaking your stack
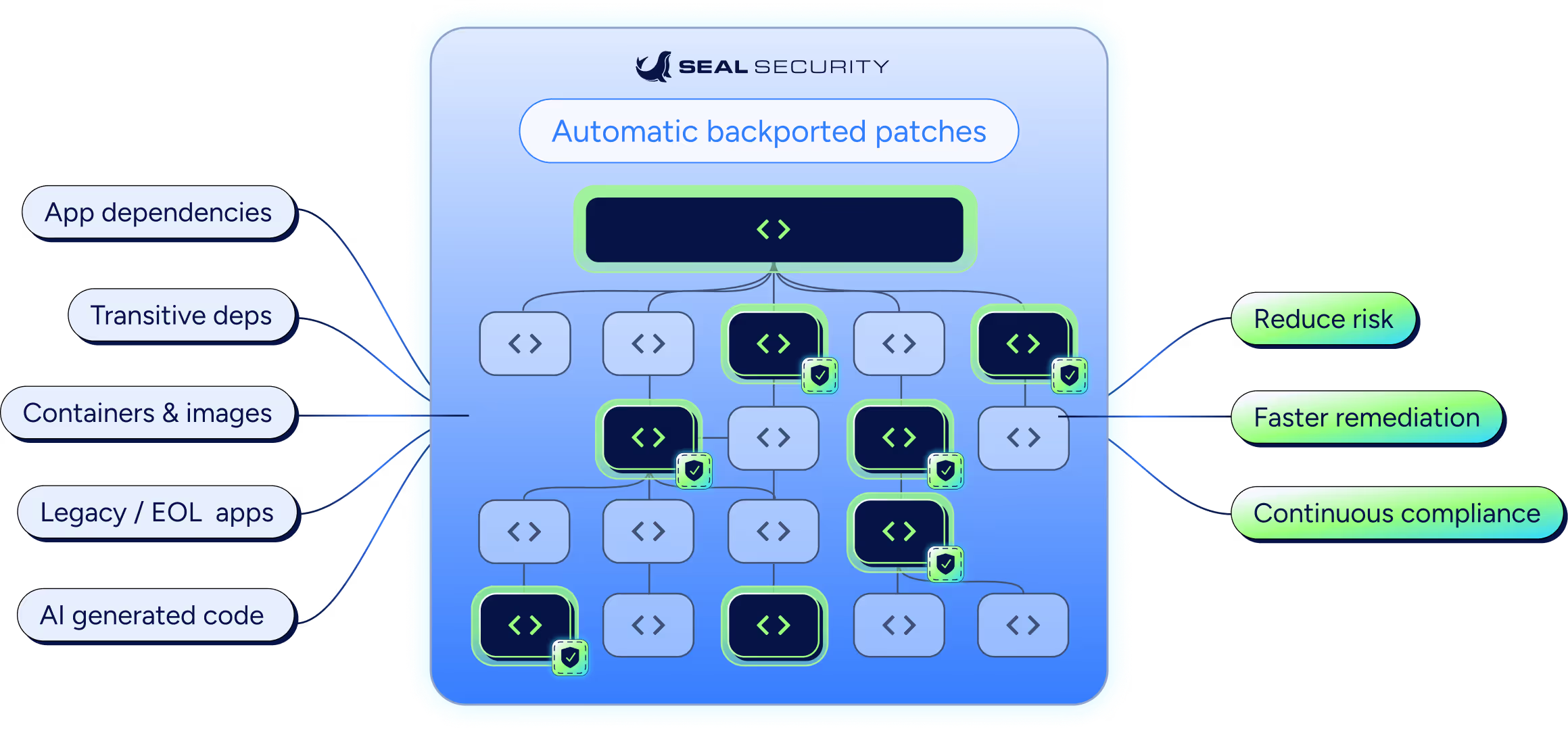
Seal fixes the unfixable across your software supply chain, backported, in-place patches for app dependencies, OS packages, and container images, so you reach audit-ready faster without upgrades or breaking changes.
Secure, scalable patches across your entire open source stack
One platform to fix every open source vulnerability
Why customers choose Seal Security
We’ll fix critical and high CVEs across your apps, OS, and containers, so you stay protected and compliant without upgrades or complex migrations.
Automatic remediation, with control
Automatically patch CVEs across the versions you already run, without waiting on engineering cycles. Keep full visibility and control with clear approvals, tracking, and confidence in every change.
No roadmap disruption
Patch in place without forcing upgrades, migrations, or breaking changes that derail planned releases. Security remediation happens in parallel, so product teams keep shipping.
Shorten the exploitation window
Reduce exposure time by moving from finding to fixing fast. Seal delivers production-ready patches for critical and high vulnerabilities on a defined SLA, so remediation does not sit in backlog.
Fix the “unfixable”
Remediate vulnerabilities in legacy, end-of-life, and hard-to-maintain components where upgrades are risky or not possible. Eliminate critical and high findings even when upstream has moved on.
Pass every security scan
Keep builds clean of critical and high findings across application dependencies, OS packages, and container images. Make scan outcomes predictable, repeatable, and easier to prove during customer reviews and audits.
Highly audited packages
Use highly audited, traceable patched packages that strengthen your supply chain. Get clear provenance and verification for each fix, so you can trust what you ship and document it when needed.
Latest research and publications
Frequently asked questions
Discover how Seal Security identifies and patches open source vulnerabilities without breaking changes.
Seal goes beyond traditional scanners by not only identifying CVEs in your source code management tools (e.g. GitHub, GitLab, and AzureDevOps), but also patching open source packages. Seal Security can also ingest scan results from popular SCA tools (e.g. Snyk and Black Duck) and widely used security tools (e.g. GitHub Advanced Security) and patch the CVEs in the open source packages.
Seal Security delivers backported security patches carefully engineered to apply only the minimal changes required to fix a vulnerability. All patches are built to be compatible with existing versions of open source packages with no added features or API modifications, ensuring maximum compatibility and minimal risk.
Seal Security uses community fixes with only the minimal necessary changes. All remediated versions undergo thorough testing and quality assurance, including manual inspection by our vulnerability research team and validation by a dedicated AI tool to ensure there are no breaking changes.
Since our platform runs at build-time, all of your existing tests run on our remediated version, providing an extra layer of assurance.
Seal supports all major distributions, including RHEL, CentOS, Alpine, and Debian.
Yes. Every image includes an SBOM (SPDX or CycloneDX format) and can be shipped with patch attestations and cryptographic signatures, making them ready for audit and continuous compliance workflows.
Seal Security supports all major Linux distributions, including Red Hat Enterprise Linux (RHEL), CentOS, Alpine Linux, Debian, and Oracle Linux
Seal helps organizations meet standards like FedRAMP, PCI DSS 4.0, NYDFS 500, and DORA by delivering secure, sealed packages and images with SBOMs and patch attestations.
Seal Security handles all critical and high-rated vulnerabilities within 72 hours of being made public.




.jpeg)